Protecting systems in the water and wastewater sector is no longer a choice – it is becoming a necessity.
Cyberattacks and radio interference can directly affect the operational stability of utilities, exposing them to financial losses and undermining their credibility and reputation.
Sabotage and disruption
Is your organization prepared?
In a recently published report by the Internal Security Agency (“Terrorist and Sabotage Threats to Critical Infrastructure 2025”), it is clearly stated that risks of a sabotage-related, hybrid, and ICT nature are increasingly affecting the water and wastewater sector as well. These are no longer theoretical scenarios—they are threats that can directly impact the operational continuity of utilities, their financial stability, and their public image.
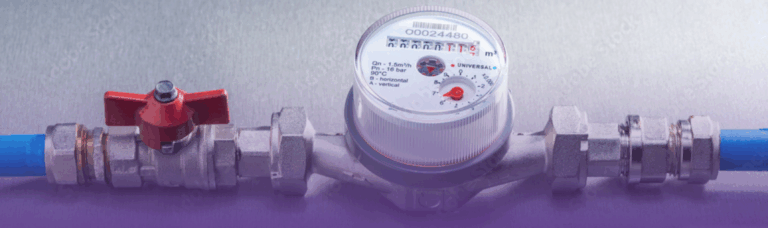
In the context of growing geopolitical tensions and increasingly sophisticated attacks on critical infrastructure, even seemingly secondary technological decisions – such as the choice of a water meter reading system – are taking on strategic importance. Today, they determine not only the efficiency of system operations, but also public trust and the financial security of water utilities.
An apparently efficient dystem
can become the weakest link
In many water and wastewater utilities, reading systems based on older radio technologies – such as walk-by radio, LoRa, or other solutions operating in unlicensed bands – are still in use. Such environments are inherently vulnerable to interference, intrusion, and manipulation, because access to them is not controlled in any way.
Unlicensed frequency bands can be used by anyone – a simple, widely available transmitting device is enough to disrupt data transmission, prevent water meter readings, and in extreme cases even deliberately falsify measurement results. This is a real risk that often goes unnoticed until serious problems occur.
Does sabotage sound abstract?
Europe shows it is a reality
In recent years – including in Poland and neighboring countries – numerous incidents related to radio transmission interference have been recorded. A widely publicized example involved so-called “radio-stop” signals emitted near railway infrastructure, which led to trains being halted and transport systems being paralyzed.
Similar activities have been observed in the energy sector, where signal interference destabilized network operations, as well as in municipal systems, leading to the loss of billing data. In many cases, experts pointed to deliberate acts of sabotage, often linked to the activities of foreign services.
The same threat landscape now also encompasses water supply infrastructure. Although less visible, it is equally critical. Systems operating in unlicensed bands are particularly vulnerable to eavesdropping, interference, and data manipulation. In some regions of Poland, the instability of such solutions has led to missing readings, billing errors, and escalating financial problems. Importantly, a radio attack does not have to be costly or complex to prove highly effective.

System silence can mean
multi-million losses
Even a short-term disruption – whether accidental or deliberate – can lead to a situation in which the system stops transmitting data. No transmission means no readings, which in turn results in a lack of settlements and invoices. The effect? A direct threat to the company’s revenues and financial liquidity.
In practice, this may include:
- the inability to bill a large number of customers,
- a sudden increase in complaints and social tensions,
- the need for a costly return to manual meter readings,
- serious financial risk for the entire organization.
All of this demonstrates that metering systems must be designed not only with functionality in mind, but above all with resilience and security. At a time when critical infrastructure is becoming a target of cyberattacks and radio interference, technological security is no longer an add-on – it is a prerequisite for stable business operations and for protecting the interests of end customers.
Sabotage and interference
Is your utility prepared?
The latest report by the Internal Security Agency (“Terrorist and Sabotage Threats to Critical Infrastructure 2025”) clearly shows that sabotage-related, hybrid, and ICT threats are no longer confined solely to the energy or transport sectors. They are increasingly affecting the water and wastewater industry as well, posing a real threat to the operational continuity of utilities, their financial stability, and their reputation.
In an environment of growing geopolitical tensions and increasingly sophisticated forms of interference with critical infrastructure, even seemingly technical decisions – such as the choice of water meter reading technology – now carry strategic importance. They determine not only system efficiency, but also customer trust and the financial security of water utilities.
A system that appears secure may be its weakest point
In many water and wastewater utilities, solutions based on older radio technologies – such as walk-by radio, LoRa, or other systems operating in unlicensed frequency bands – are still in use. Such environments are inherently easy to disrupt and difficult to secure, because access to them is not subject to real control.
Unlicensed bands are widely accessible – often a simple transmitting device is enough to disrupt data transmission, prevent water meter readings, or even deliberately influence measurement results. This is a threat that may remain unnoticed until serious operational problems occur.
Sabotage is not theory
European examples speak for themselves
In 2023, numerous cases of radio transmission interference were recorded in Poland and neighboring countries. One of the most well-known involved so-called “radio-stop” signals emitted near railway infrastructure, resulting in trains being stopped and traffic brought to a standstill.
Similar incidents occurred in the energy sector, where signal interference destabilized networks, as well as in municipal systems, leading to the loss of billing data. In many cases, deliberate acts of sabotage were indicated, often linked to the activities of foreign services.
The same threat model now also applies to water supply infrastructure. Although less visible, it is equally critical. Systems operating in unlicensed bands are particularly vulnerable to eavesdropping, interference, and data manipulation, which in practice can lead to missing readings, billing errors, and growing financial chaos. Importantly, a radio attack does not have to be costly or complex to cause serious consequences.
Silence in the system can mean real financial losses
Even a short-term disruption—whether accidental or deliberate—can cause the system to stop transmitting data. No transmission means no readings, which directly translates into the inability to issue invoices. As a result, there is a real threat to the company’s financial liquidity.
In practice, this may lead to:
- the inability to bill a large number of customers,
- a sharp increase in complaints and social tensions,
- the need for an emergency return to manual meter readings,
- serious financial risk for the entire utility.
All of this shows that metering systems must be designed with resilience and security in mind—not solely functionality. In a world where critical infrastructure is increasingly targeted by cyber and radio disruptions, technological security is no longer a choice—it has become a prerequisite for stable operations and for protecting the interests of end users.
Can a Meter Reading System Be Manipulated? Unfortunately, Yes – Even from a neighboring building
Legacy solutions based on local radio communication are among the most vulnerable elements of infrastructure. In practice, basic electronic equipment and technical know-how are sufficient to eavesdrop on transmissions, disrupt data transfer, generate false readings, or introduce noise into billing systems.
The consequences of such actions can be serious: from incorrect bills and missing data, through a surge in complaints, to loss of customer trust and real financial losses. In extreme cases, this can lead to destabilization of the entire organization and social tensions.
Technology and Cybersecurity as a Real Response to New Threats
In the face of growing risks, stationary communication solutions based on NB-IoT, operating in a controlled, closed transmission environment—such as through the use of a private APN and in cooperation with a trusted network operator—are becoming increasingly important. This approach significantly reduces the threats characteristic of unlicensed bands and makes it possible to maintain full control over data flows.
As a manufacturer of electronics and IoT solutions, we point to key elements that are fundamental from the perspective of cybersecurity and regulatory compliance:
- communication in licensed frequency bands, minimizing the risk of interference and external tampering,
- elimination of local communication interfaces, reducing the possibility of unauthorized access,
- full end-to-end encryption of data transmission,
- continuous real-time data availability, regardless of environmental conditions,
- 24/7 monitoring and technical support, enabling rapid response in crisis situations.
Solutions designed in this way not only address current threats but also support long-term risk management in the water and wastewater sector.
Cybersecurity
in Water Utilities –
The Foundation of Long-Term Stability
In a special report prepared by the Internal Security Agency, it was clearly stated that water and wastewater infrastructure constitutes a potential target for cyberattacks, primarily due to insufficient protection of local systems. The authors of the report note that many installations rely on technologies from before the era of widespread internet access, which makes them particularly vulnerable to hybrid threats.
Attacks may target both transmission systems and the ICT layer, leading to operational paralysis, financial losses, and serious reputational consequences for entities responsible for delivering critical services. In this context, digital security ceases to be an add-on—it becomes the foundation of stable operation for modern water utilities.
In the face of growing threats to critical infrastructure, including water supply systems, abandoning investment in security leads to serious, multi-level consequences. These include the risk of billing disruptions, vulnerability to sabotage, potential legal sanctions, as well as loss of reputation and public trust. Today, cybersecurity is not an optional add-on—it is a fundamental requirement for the operation of every water utility.
In a world of escalating geopolitical tensions and rapidly evolving technological threats, failure to implement stable and secure meter reading systems exposes water utilities to tangible losses—financial, operational, and reputational. This challenge goes beyond technology alone. It is about responsibility for the continuity of water supply, infrastructure security, and public trust. Unsecured systems become easy targets, and the consequences can shape the future of the entire organization.
Do not wait until a crisis occurs. Discover our intelligent and secure technology solutions today.
Plum helps ensure the security of infrastructure
For years, Plum has been developing modern solutions for the water and wastewater sector, designed with security in mind. The MacIQ WM telemetry module operates in licensed frequency bands, uses NB-IoT to ensure connectivity even in challenging locations, and offers configurable alarms that detect tampering and attempted removal. As a result, water infrastructure remains secure and under constant control.

